
Vulnerability Management
Here are the key steps involved in a Vulnerability Management
1. Scope Definition: Determine the scope of the assessment, including the systems, networks, and applications that will be evaluated. Consider both internal and external assets.
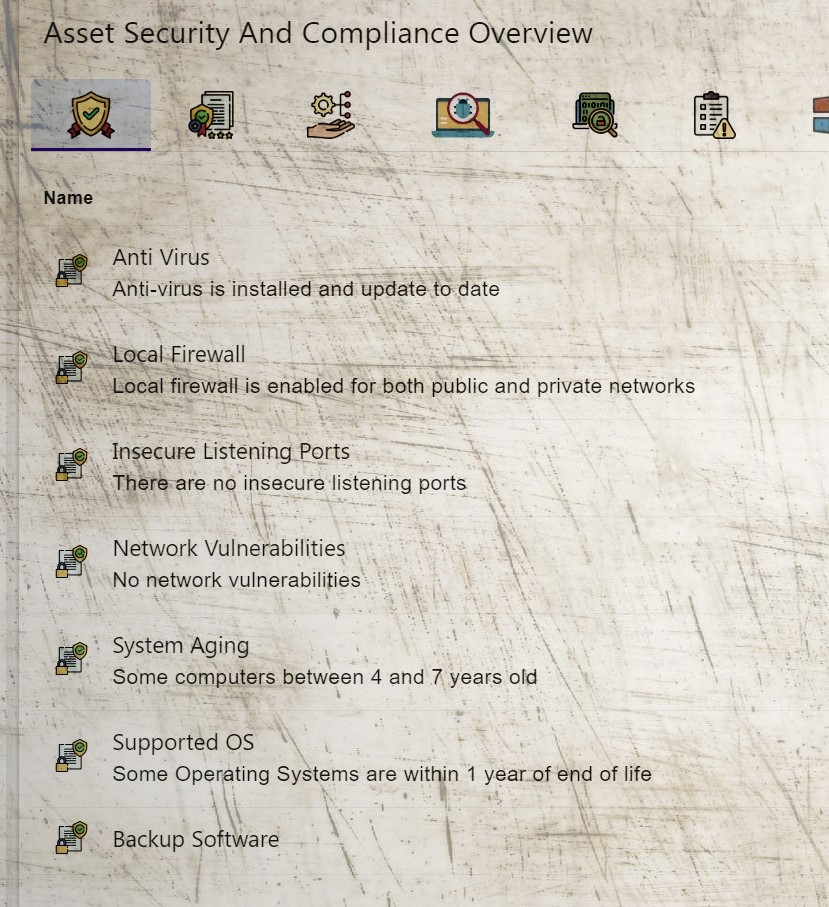
2. Asset Inventory: Create an inventory of all assets within the defined scope. This includes hardware, software, operating systems, databases, and network devices.
3. Vulnerability Scanning: Perform automated vulnerability scans using specialized tools. These tools scan the assets for known vulnerabilities based on a database of vulnerabilities and associated patches.
4. Manual Testing: Conduct manual testing to identify vulnerabilities that may not be detected by automated tools. This involves in-depth analysis and verification of identified vulnerabilities.
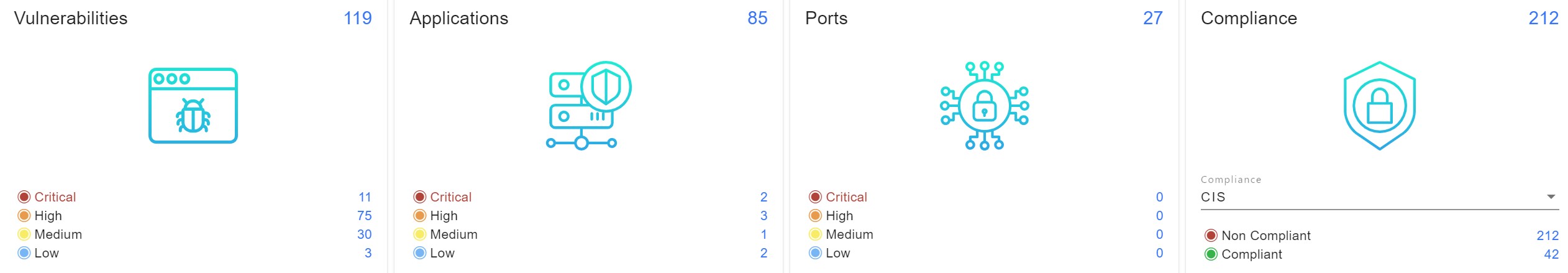
5. Vulnerability Prioritization: Analyze and prioritize vulnerabilities based on their severity, potential impact, and exploitability. Common vulnerability scoring systems, such as the Common Vulnerability Scoring System (CVSS), are often used for this purpose.
6. Risk Assessment: Assess the potential risks associated with the identified vulnerabilities, considering the likelihood of exploitation and the potential impact on the organization’s systems, data, and operations.
7. Reporting: Document the findings of the vulnerability assessment, including a detailed list of vulnerabilities, their severity, and recommended actions for remediation. The report should provide clear and actionable information for stakeholders.
8. Remediation Planning: Develop a remediation plan to address the identified vulnerabilities. This plan should prioritize the most critical vulnerabilities and outline the steps and resources required for remediation.
9. Remediation and Verification: Implement the necessary measures to remediate the vulnerabilities based on the prioritized plan. After remediation, perform verification checks to ensure that vulnerabilities have been effectively mitigated.
10. Ongoing Monitoring: Implement a continuous monitoring process to identify new vulnerabilities and ensure that systems remain secure. This may include regular vulnerability scanning, penetration testing, and system patching.
It is important to note that vulnerability assessments should be conducted periodically to account for the evolving threat landscape and the introduction of new vulnerabilities. Organizations may also consider engaging external security professionals or consultants with expertise in vulnerability assessments to ensure comprehensive and objective evaluations.
